ESET experts have come up with a new spy platform
1 min read
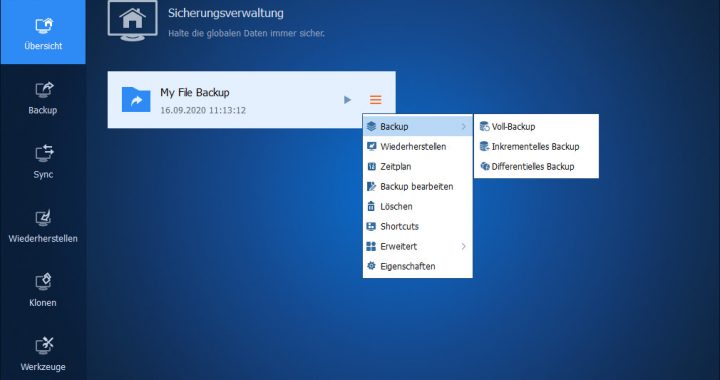
The Attor platform has a complex architecture and a number of detection and analysis features. It is modular in structure: it consists of a central control unit (dispatcher) and loadable modules (plugins) that use the management unit to perform basic functions. These plugins arrive on the hacked computer as encrypted DLLs and are only fully assembled later in memory.
Two of the capabilities deployed by Attor modules are truly unique due to their rare characteristics: network communication and GSM mapping. To maintain anonymity and prevent traceability, the platform uses the Tor (TOR, The Onion Router) protocol to access the remote control server.

The most exclusive module in the Attor’s arsenal collects information about the connected modem and telephone devices, as well as the connected drives and the files on them. According to ESET researchers, the primary purpose of this is to map GSM devices connected to the computer through the serial port. Attor uses so-called “AT commands” to communicate with the device and to retrieve identification codes.
ESET identifies the threat as Win32 / Attor and Win64 / Attor, and further details on the analysis can be found on the Welivesecurity website.
Personally, we believe that the ESET Internet Security is one of the best out there currently. And, if you are looking to grab a copy, you can get a cheap ESET Internet Security 1 Device 1 Year Key on Bzfuture now!